by Julia Weifenbach | Mar 14, 2023 | Blog, ThreatQ Profiles
Women in Cybersecurity Stacey AntoninoKela – VP of Strategic Alliances and Partnerships Where do you work?Kela How long have you worked here?10 months What do you enjoy most about your job and company?Two things: I love that we have a great mix of talent and...

by Emily Jacob | Mar 13, 2023 | Blog, ThreatQ Profiles
Women in Cybersecurity Jana LindThreatQuotient – Regional Sales Director Where do you work?ThreatQuotient How long have you worked here?7 years and counting What do you enjoy most about your job and company?The people. ThreatQuotient has a unique variety of...

by Julia Weifenbach | Mar 9, 2023 | Blog, ThreatQ Profiles
Women in Cybersecurity Celine Gajnik-KinnooThreatQuotient – Global Marketing Director Where do you work?ThreatQuotient How long have you worked here?I have been at ThreatQuotient for more than 6 years. What do you enjoy most about your job and company?Working...
by Julia Weifenbach | Mar 8, 2023 | Blog, ThreatQ Profiles
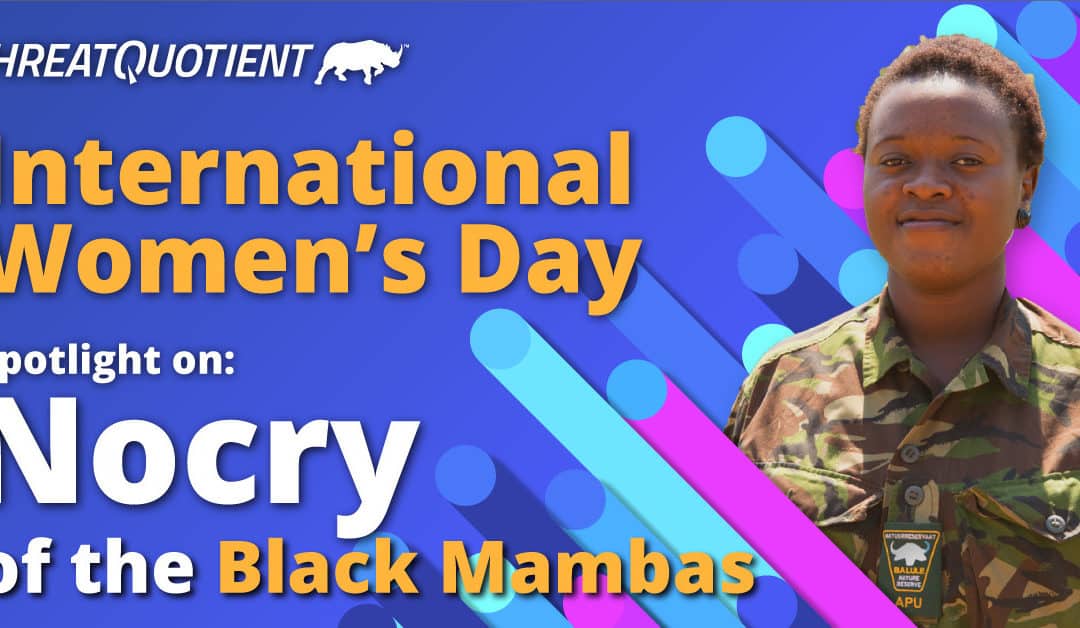
International Women’s Day! Nocry Mzimba Black Mambas – Sergeant Where do you work? Black Mambas How long have you worked here? From April 2013 which is makes it 10 years now. I come from the first Mambas intake, and this year we are...

by Julia Weifenbach | Mar 7, 2023 | Blog
Celebrate Women in Cybersecurity with Us! Julia Weifenbach There’s a lot to be proud of as part of the ThreatQuotient Crash, but one thing I’m particularly proud of is our commitment to recognizing and encouraging women in cybersecurity. We do this consistently...

by Guest Blog | Feb 28, 2023 | Blog
Importance of great communication Tanuj Gandhi In all relationships, issues can arise. The key to solving those issues is to have a clear understanding of the issue itself. For instance, when a customer reports an issue it is critical to listen to the customer with...